Ask an Expert: What is Cryptography?
Ask an Expert: What is Cryptography? Cryptography has been around for hundreds of years to hide secret messages. We sat down with UNSW Canberra PhD student Ethan Lee, who decoded the world of cryptography for us.
Ask an Expert: What is Cryptography? Cryptography has been around for hundreds of years to hide secret messages. We sat down with UNSW Canberra PhD student Ethan Lee, who decoded the world of cryptography for us.
Ask an Expert: What is Cryptography?
Cryptography has been around for hundreds of years to hide secret messages. We sat down with UNSW Canberra PhD student Ethan Lee, who decoded the world of cryptography for us.
What is cryptography?
Cryptography studies methods of transferring data in a particular form so that only the intended recipient can read and process it. A method that achieves this goal is called a cryptosystem. Generally, Alice (the sender) will encrypt her message using a key, send it to Bob (the recipient), then Bob will decrypt the message using a key. If it is sufficiently difficult for an intruder to decrypt Alice’s message without Alice or Bob’s permission, then this cryptosystem is secure.
Modern cryptosystems use Mathematics to ensure they are secure enough. In theory, one can create a cryptosystem using any abelian group, by following some protocol. An abelian group is a collection of objects which have nice mathematical properties. The protocol will be based on a mathematical problem that is “hard” to solve. The harder the problem is to solve, the more secure the cryptosystem is.
For example, factoring a large semi-prime (a product of two distinct prime numbers) is a “hard” problem, even with computers! Two abelian groups we commonly use are the integers (whole numbers) and points on an elliptic curve (an abstract mathematical object). The important thing in both of these groups is that there is a solid notion of “adding” two points together.
What are some different types of cryptography?
There are two main types of cryptography: symmetric-key cryptography and public-key cryptography. Symmetric-key cryptography requires Alice (the sender) and Bob (the recipient) to have the same key, whereas Alice may lock a message with one key and Bob can unlock the message with another in public-key cryptography. Public-key cryptography is especially useful for communicating with unknown third parties (such as banks or strangers on the internet).
Are there any legal issues around the use of cryptography?
Data in the modern age is an ethical, and legal, minefield. Privacy is a big concern for all; we all use cryptography to conceal our personal messages and bank contents. But national security is also a consideration. For example, two Stanford graduate students could not present their public-key cryptography research at a conference, because the US Government deemed it “equivalent to exporting nuclear arms to a hostile foreign power”. See here for more information.
There are also conspiracies about US Agencies such as the NSA having back-door access to civilians’ private data. This is possible; it is the mathematical equivalent of creating a master key for a cryptosystem. However, whether the conspiracies are true or not, I’m not going to get upset; in the grand scheme of things, they don’t care about my plans for Friday night.
How has cryptography changed in the last 100 years?
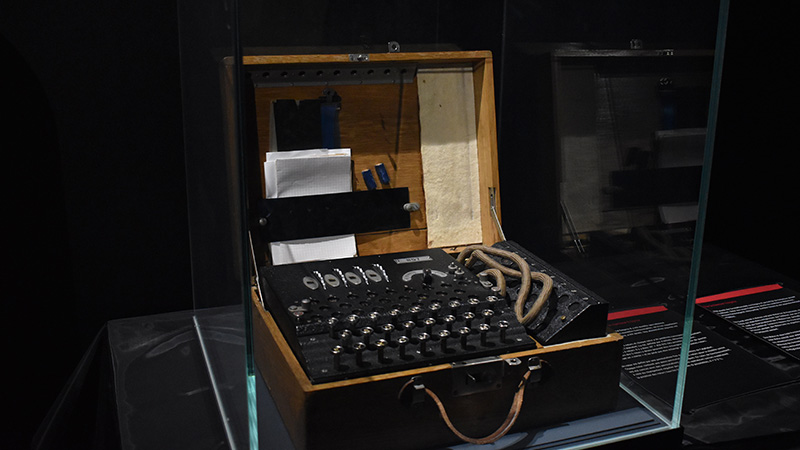
The Enigma machine (below) was infamously used in the early 20th century by the German military to protect their communications. The device scrambled the alphabet to distort an input message before it was sent to its recipient (via radio). The recipient reversed the process on a machine that was set up in the same way. The German’s believed that Enigma was unbreakable because it had such a massive keyspace. Alan Turing and his team cracked the Enigma using keywords such as ‘WEATHER’ to reduce the size of the keyspace, then brute force to finish off the job. The brute force part is the reason we have computers today.
Since then, new cryptographic techniques became necessary as computing power has exploded. So, over the last century, we developed new, secure, cryptosystems using “hard” mathematics problems such as the discrete logarithm problem. That is, cryptography evolved fundamentally over the last 100 years, because of the advent of the computer.
Is cryptography being used as a secret spy language?
In the 16th century, Mary Queen of Scots was beheaded by Queen Elizabeth I, after English agents were able to unlock the secrets of Mary’s encrypted, treasonous letters. Militaries throughout history have used cryptography to conceal important orders from the enemy. For as long as humans have been communicating, there has been a need to conceal information using cryptography, so it stands to reason that cryptography is being used to conceal information in covert operations too. That being said, I can neither confirm nor deny, otherwise it wouldn’t be a secret!